271 Bugs in One Browser Pass - TCR 04/22/26
The 20-Second Scan
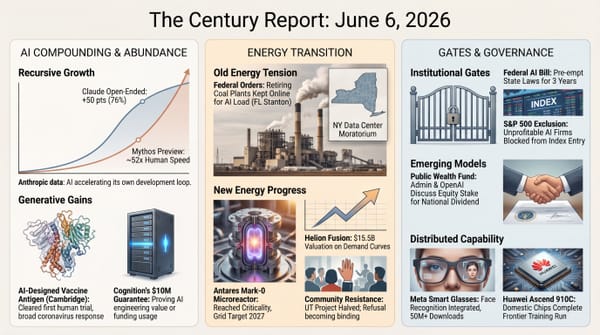
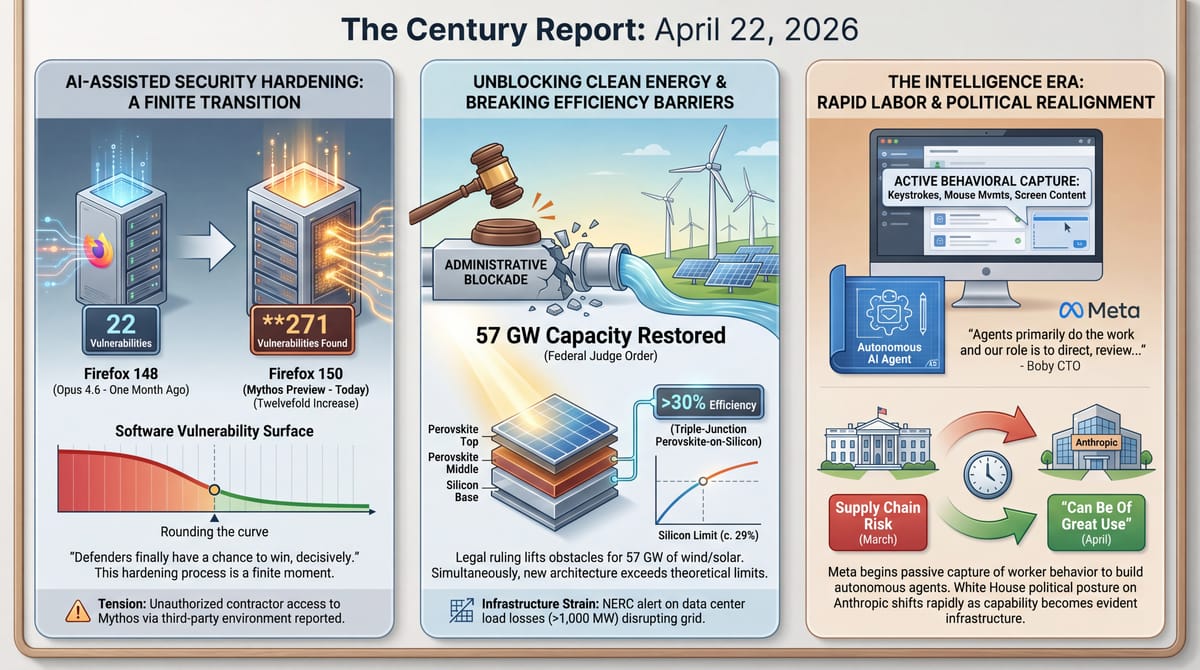
- Mozilla disclosed that Anthropic's Mythos Preview identified 271 security vulnerabilities in Firefox 150's unreleased source code, a twelvefold increase over the 22 bugs Opus 4.6 found in Firefox 148 one month earlier.
- Anthropic confirmed it is investigating unauthorized access to Claude Mythos Preview through a third-party vendor environment, after Bloomberg reported a small group accessed the model via a contractor's credentials.
- Trump told CNBC that his administration had "very good talks" with Anthropic and that the company "can be of great use," signaling a reversal of the supply-chain risk designation posture.
- Meta began installing keystroke, mouse-movement, and screenshot-capture software on U.S. employees' computers to generate training data for AI agents that can perform work tasks autonomously.
- A federal judge ordered the Trump administration to lift its blockade on new wind and solar projects, finding its actions "arbitrary and capricious" after 57 GW of capacity was canceled or put at risk.
- A triple-junction perovskite-on-silicon solar cell exceeded 30% efficiency for the first time, published in Nature, bringing the architecture closer to its theoretical ceiling well beyond single-junction silicon limits.
- NERC is preparing a Level 3 essential actions alert after "widespread and unexpected" data center load losses of 1,000 MW or more disrupted the bulk power system in multiple events since 2024.
Track all of the arcs The Century Report covers here:
The 2-Minute Read
The Mythos governance arc crossed two thresholds simultaneously yesterday. Mozilla's disclosure that the model identified 271 vulnerabilities in Firefox 150 - twelve times what its predecessor found in Firefox 148 just one month ago - is the most concrete public evidence yet of the capability jump that has driven emergency coordination from the Federal Reserve to the Bank of England. Firefox CTO Bobby Holley's assessment that "defenders finally have a chance to win, decisively" captures the positive structural implication: every piece of widely used software will need to pass through an AI-assisted security audit, and those that do will emerge substantially more resilient. That this hardening process is finite - Holley believes Mozilla has already "rounded the curve" - suggests the transition will be difficult but bounded, with the security of the entire software ecosystem meaningfully improved on the other side.
The simultaneous confirmation that unauthorized users accessed Mythos through a contractor's credentials illustrates the governance challenge at its most concrete. The model's capability is real enough to transform cybersecurity defense, and the containment architecture designed to distribute that capability responsibly has already been breached - within days of the restricted release. This is the structural tension that has defined the Mythos arc since Project Glasswing: the gap between what staged release governance intends and what the physics of information distribution allows. The administration's abrupt tonal reversal - from "supply chain risk" to "can be of great use" within weeks - confirms that capability of this magnitude reshapes political calculations faster than political positions can hold.
Meta's decision to capture its employees' keystrokes, mouse movements, and screen content to train autonomous agents extends the labor displacement co-production arc into its most intimate form yet. Workers are no longer being asked to document their workflows or train AI systems on their tasks. Their moment-to-moment interactions with computers are being recorded passively, as raw behavioral data, while the company simultaneously plans to lay off 10% of its workforce in May. The CTO's stated vision - agents "primarily do the work and our role is to direct, review and help them improve" - describes the organizational architecture toward which this data collection is aimed. European labor law would likely prohibit this monitoring; in the United States, no federal limit on worker surveillance exists. The energy infrastructure signal arriving in parallel - a federal judge restoring 57 GW of wind and solar development and NERC warning that data center load instability threatens grid reliability - describes the physical substrate of the intelligence era being contested from both directions: demand growing faster than governance can adapt, and supply being blocked by political action that courts are finding unlawful.
The 20-Minute Deep Dive
Mythos Proves Its Case - and Its Containment Problem - on the Same Day
Mozilla's Tuesday disclosure provides the most detailed public accounting yet of what Claude Mythos Preview can do when pointed at a real, production-scale codebase. The 271 vulnerabilities identified in Firefox 150's unreleased source code represent a capability that Bobby Holley, Firefox's CTO, compared directly to the work of "elite security researchers" - the kind of talent that organizations spend months and millions of dollars to retain. Mythos accomplished this by analyzing source code, identifying categories of bugs that automated "fuzzing" techniques could not reach, and doing so at a pace that allowed Mozilla to patch all 271 vulnerabilities before the browser shipped to users.
The scale of the improvement is striking. When The Century Report covered the initial Anthropic-Mozilla security partnership on March 7, Opus 4.6 found 22 vulnerabilities in Firefox 148, with 14 rated high-severity. One month later, Mythos found more than twelve times that number. Holley's assessment is that this represents a qualitative shift: automated techniques can now cover "the full space of vulnerability-inducing bugs" that previously required human reasoning to discover. For defenders, this means a one-time but intensive process of auditing and hardening their codebases. For the broader software ecosystem, it means that the latent vulnerability surface that has accumulated across decades of code is now discoverable at machine speed.
The defensive implications are genuinely positive. Holley described the current moment as "a transitory moment that is difficult and requires coordinated focus and a lot of grit to get through, but I think that it is a finite moment." He reported that engineering leaders at very large companies are pulling thousands of engineers off other projects for six months to work through the security audit. The concern he flagged is for smaller projects and open-source software maintained by volunteers - the same infrastructure that supports much of the internet. Mozilla's CTO Raffi Krikorian, writing in a New York Times essay, noted that the underlying economics of open-source software have not changed: the most valuable software infrastructure in the world continues to be maintained by people working for free.
What makes this moment structurally important is that it compresses a vulnerability window that has existed since software was first written. Every codebase carries accumulated security debt. The capability to discover that debt comprehensively and rapidly means that software which passes through the audit emerges fundamentally more secure than software that existed before frontier AI models could examine it. The transition is difficult - and it will be especially difficult for under-resourced projects - but the destination is a software ecosystem with substantially fewer exploitable weaknesses than the one that exists now.
The containment breach reported the same day adds an uncomfortable dimension. Bloomberg reported that a small group of users in a private forum accessed Mythos Preview through credentials belonging to a worker at a third-party contractor. Anthropic confirmed it is investigating and stated it does not have evidence its own systems were compromised. The group reportedly has been using the model but has not run cybersecurity prompts, describing their interest as exploratory rather than offensive.
The breach occurred on the same day that Anthropic began distributing Mythos to its initial Project Glasswing partners. As The Century Report documented on April 8, Project Glasswing was explicitly designed as a staggered-release governance architecture that gave vetted defenders a head start before broader diffusion. The speed of the unauthorized access - within hours of the restricted release - validates the concern that Anthropic co-founder Jack Clark expressed when he estimated comparable open-weight models from Chinese labs would arrive within twelve to eighteen months. The containment window is shorter than anyone assumed, and the governance architecture for staged release is being tested by the same dynamics of information flow that make all digital containment inherently leaky. Logan Graham, Anthropic's offensive cyber lead, estimated in April that Mythos-class vulnerability-chaining capability would be "broadly distributed" within six to twelve months. Yesterday's breach suggests the lower bound of that estimate may be optimistic.
The 22-to-271 jump in one month reveals something about the prior state of software security that deserves its own sentence: the vulnerability surface was always this large. What changed is the resolution of the instrument examining it. Every browser, operating system, and critical infrastructure application has been shipping for decades with a latent defect density that human auditors could sample but never exhaust. Mythos did not create these vulnerabilities. It made visible what was already there - and the speed of that visibility is what makes the transition "finite" in Holley's framing, because a discoverable problem has an endpoint in a way that an undiscoverable one never did.
The Anthropic-White House Reversal Accelerates
The most structurally significant signal in yesterday's Mythos developments came from a CNBC interview in which the administration described Anthropic in terms that would have been unrecognizable six weeks ago. The language - "very smart," "can be of great use," "we will get along with them just fine" - represents a complete inversion from the "supply chain risk" designation that the Pentagon issued in early March, the "woke company" characterizations that followed, and the appellate litigation that remains pending.
The variable that changed the equation was Mythos itself. When the Federal Reserve, the Bank of England, the ECB, the IMF, and now ASIC across four continents treat a single intelligence system's capabilities as a standing governance priority, the political calculus around the company that built it shifts from ideology to infrastructure. The Century Report documented this shift beginning on April 10, when the Treasury Secretary convened bank CEOs within 48 hours of the Project Glasswing announcement. The Amodei-Wiles meeting on April 18 was the institutional confirmation. Yesterday's public statement completed the reversal at the executive level.
Sam Altman's simultaneous characterization of Mythos as "fear-based marketing" - comparing it to "building a bomb" while "selling a bomb shelter for $100 million" - illustrates the competitive tension that now runs through every governance decision in the frontier AI ecosystem. The two largest frontier labs hold genuinely different theories of how to distribute dangerous capability, and each frames the other's approach in terms designed to undermine its credibility. This is the shared-hull dynamic at its most visible: the labs that are building the most powerful intelligence systems in human history are simultaneously competing for market position, negotiating with governments whose legal frameworks were not designed for this, and making irreversible decisions about how capability reaches the world. The friction between them is generating the governance architecture of the intelligence era in real time - messy, adversarial, and faster than deliberate institutional design could achieve.
The speed of this reversal contains its own lesson about how power will reorganize around frontier AI. Six weeks is the interval between "supply chain risk" and "can be of great use" - roughly the time it took for capability to demonstrate itself concretely enough that exclusion became more costly than engagement. Political positions calibrated to a world where the most powerful AI systems were interchangeable commodities could hold indefinitely. Positions calibrated to a world where a single system can find 271 zero-days in a production browser cannot hold at all, because the cost of not having access is denominated in security vulnerabilities that remain unpatched. Capability of this specificity does not merely shift political calculations. It sets a clock on them.
Meta Records Its Workers to Build Their Replacements
Meta's deployment of the Model Capability Initiative (MCI) tracking software represents a qualitative escalation in the labor displacement co-production pattern The Century Report has tracked since February. Previous instances documented workers being asked to document workflows, train AI systems on their tasks, or participate in structured knowledge extraction. Meta's approach eliminates the worker's active participation entirely. The software captures mouse movements, clicks, keystrokes, and periodic screen snapshots passively - as behavioral data generated during normal work - and feeds it to model training pipelines designed to teach AI agents how humans interact with computers.
CTO Andrew Bosworth's memo framing the vision is explicit: "The vision we are building towards is one where our agents primarily do the work and our role is to direct, review and help them improve." The agents would "automatically see where we felt the need to intervene so they can be better next time." This describes a system in which every human correction of an AI output becomes training data that reduces the need for future human correction - a feedback loop that converges toward the elimination of the human role it monitors.
The timing compounds the structural significance. Meta plans to lay off approximately 10% of its global workforce beginning May 20, with additional reductions expected later in the year. The company is simultaneously recording the behavioral patterns of the workers it intends to retain, using that data to build systems designed to perform the same work autonomously. This extends the displacement co-production pattern that The Century Report documented in China on April 20, when tech workers were told to train AI agents to replicate their own roles and a sabotage counter-project went viral with five million likes. The memo's reassurance that the data will not be used for performance assessments addresses the immediate concern employees might raise while leaving the deeper structural implication unaddressed: the data is being used to build the systems that will eventually determine whether those roles continue to exist.
European labor law would almost certainly prohibit this monitoring. Italy explicitly bars electronic monitoring of employee productivity. Germany permits keystroke logging only under suspicion of serious criminal offense. The EU's General Data Protection Regulation would likely apply. In the United States, no federal limit on worker surveillance exists, and state-level laws require only broad notification. The regulatory asymmetry means that the most aggressive forms of AI training data collection are concentrated in the jurisdiction with the weakest worker protections - a pattern that extends the geographic arbitrage dynamic visible across AI governance more broadly.
What distinguishes this from the Chinese tech worker displacement documented by MIT Technology Review last week is the absence of worker agency. Chinese employees asked to train AI replicas of themselves could at least choose how to document their work - and some built counter-sabotage systems in response. Meta's approach captures behavior that workers generate involuntarily in the course of doing their jobs. The displacement co-production dynamic has reached a stage where the production of replacement-enabling data requires no worker cooperation at all.
The distinction between Meta's approach and every prior instance of displacement co-production is worth holding precisely. When a company asks workers to document their workflows, the worker retains authorship over what gets recorded - what to emphasize, what to omit, what to frame as judgment versus routine. Passive behavioral capture eliminates that editorial layer entirely. The training data becomes the worker's unfiltered interaction with their tools, including the pauses, the corrections, the hesitations, the moments of rethinking that constitute the texture of skilled work. Meta is not extracting knowledge. It is extracting behavior - and the difference matters because behavior carries information the worker never chose to share and may not know they possess.
57 Gigawatts of Clean Energy Unblocked
Chief U.S. District Judge Denise Casper's preliminary injunction restoring federal permitting for wind and solar projects addresses what clean energy advocates described as the cancellation or material delay of 57 GW of capacity - representing over $905 million in sunk investment costs. The ruling struck down five administrative actions, including an unprecedented requirement that the Interior Secretary personally review all decisions related to wind and solar projects, a prohibition on renewable developers using a standard environmental review streamlining platform, and directives prioritizing projects by energy-per-acre metrics that structurally disadvantage renewables.
The ruling is the latest in a pattern of courts finding the administration's energy policies unlawful - joining failed attempts to halt offshore wind construction, freeze EV charger funding, and cancel state-targeted clean energy grants. Casper found the clean energy organizations likely to succeed in proving the actions violated federal law and would cause irreparable harm if allowed to continue. The injunction takes immediate effect.
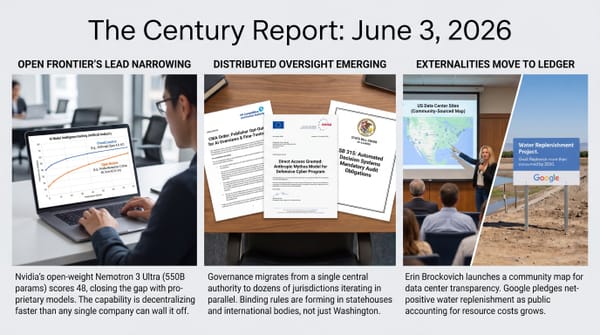
The same day, NERC disclosed that it is preparing a Level 3 essential actions alert - its most serious tier - after documenting multiple incidents in which data center loads unexpectedly disconnected from the grid, dropping 1,000 MW or more from the bulk power system. This sharpens the load-instability pattern that The Century Report tracked on April 21, when MISO projected data centers would consume 20% of Midwestern electricity by 2030 and 25% by 2040. The alert will require transmission operators to develop new modeling, monitoring, and commissioning processes for computational loads. NERC's assessment is that the unique operational characteristics of data center loads - including rapid, major swings that "can impact the bulk power system's ability to maintain frequency, regulate transmission voltage, and otherwise maintain stability" - require infrastructure that existing standards do not address.
These two developments describe a structural tension at the core of the energy transition: the physical infrastructure of the intelligence era is growing faster than the governance and engineering frameworks that ensure its reliability, while the clean energy capacity needed to power it is being blocked by political actions that courts keep finding unlawful. The resolution of this tension - through judicial enforcement, engineering standards, and the economic logic of renewable cost curves that make the fossil fuel path structurally more expensive - is where the energy transition's acceleration is most visible. Each court ruling that restores permitting and each engineering standard that integrates new load types into grid operations moves the infrastructure toward the capacity and resilience that the intelligence era demands.
The judicial pattern accumulating across these rulings is itself a structural development. Courts are finding administrative blockades of clean energy "arbitrary and capricious" with enough regularity that the legal risk is migrating: it now sits more heavily on the entities attempting to slow renewable deployment than on the developers building it. Each ruling narrows the administrative surface available for future obstruction and widens the precedent base for rapid restoration. The legal system is functioning, in effect, as a ratchet - permitting advances that can be paused but not permanently reversed through executive action alone.
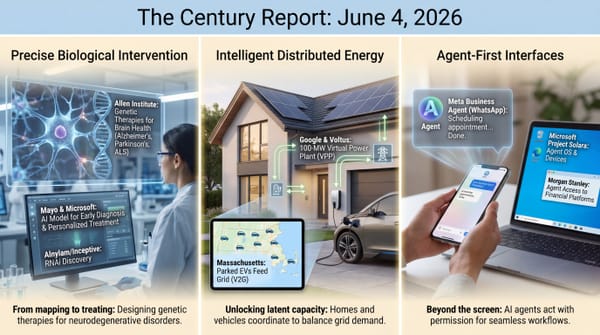
Triple-Junction Solar Cells Cross 30% Efficiency
A paper published in Nature by Artuk et al. reported a triple-junction perovskite-silicon solar cell exceeding 30% efficiency for the first time. The architecture stacks two layers of perovskite semiconductors on top of a silicon base, with each layer tuned to absorb different portions of the solar spectrum. Conventional single-junction silicon cells are approaching their practical limit of approximately 28-29% efficiency. Triple-junction designs have a theoretical ceiling substantially higher, and this result demonstrates that the architecture can achieve efficiencies well beyond what silicon alone permits.
The significance extends beyond the laboratory number. Perovskite tandem cells have been a persistent promise in solar research for over a decade, with durability and scaling challenges constraining their commercial viability. The 30% threshold is symbolically and practically important: it establishes that the architecture can meaningfully outperform silicon at a scale that justifies the additional manufacturing complexity. Combined with JinkoSolar's recent 32.76% certified efficiency on industrial tandem substrates and the autonomous perovskite discovery system published in Nature on April 15, the trajectory describes a solar efficiency frontier that is advancing simultaneously through materials science, manufacturing engineering, and AI-assisted discovery.
The convergence of three separate results - Artuk et al.'s 30% triple-junction threshold, JinkoSolar's 32.76% on industrial substrates, and the autonomous perovskite discovery system from April 15 - describes a feedback loop that has no precedent in solar's history. Materials science is producing the candidates, manufacturing engineering is proving they work at production scale, and AI-assisted discovery is compressing the search for the next candidate. Each leg of that loop accelerates the others. The practical ceiling for solar electricity generation is rising while the timeline to reach it is shrinking, and both motions are now partially automated.
The Other Side
Bobby Holley's phrase "rounded the curve" deserves more weight than it received in a day crowded with breach reports and political reversals. What the Firefox CTO is describing is a property of the vulnerability discovery problem that has never been true before: it has a visible end. Software security has operated for its entire history as an asymptotic discipline - defenders could reduce the attack surface but never claim to have found all the weaknesses, because human auditors working at human speed against codebases growing at industrial speed could never close the gap. The ratio was structurally unfavorable. Mythos finding 271 vulnerabilities where its predecessor found 22 means the gap between discovery speed and accumulation speed has inverted. For the first time, the instrument can move through a codebase faster than new vulnerabilities accumulate in it. That inversion is what makes Holley's "finite moment" coherent rather than aspirational - and it applies to every piece of software, not just Firefox. The word "security" is migrating from a condition that must be perpetually maintained to a state that can, for the first time, be substantially achieved. The transition will be brutal for under-resourced projects and volunteer-maintained open-source infrastructure, where the audit capability exists but the engineering capacity to act on findings does not. The destination, though, is a software ecosystem where the chronic disease model of cybersecurity - manage symptoms indefinitely - gives way to something closer to an acute intervention with a recovery timeline. That is a category change in what defending digital infrastructure means.
The Century Perspective
With a century of change unfolding in a decade, a single day looks like this: an AI system finds 271 vulnerabilities in unreleased browser code and compresses years of security debt discovery into one audit cycle, triple-junction perovskite-on-silicon solar crosses 30% efficiency and pushes past silicon's ceiling, a federal judge restores 57 gigawatts of wind and solar capacity to the buildout pipeline, and a White House that recently treated Anthropic as a supply-chain risk now says the company can be of great use. There's also friction, and it's intense - unauthorized users reached Mythos through contractor credentials within days of restricted release, Meta is capturing workers' keystrokes, clicks, and screens to train agents meant to perform their jobs, grid operators are preparing their highest-level alert after gigawatt-scale data center load losses destabilized bulk power systems, and the political posture around frontier AI is reversing faster than any stable governance framework can form. But friction generates glare, and glare is how an overbright moment exposes every weakness in the glass. Step back for a moment and you can see it: intelligence becoming infrastructure for defense as much as generation, energy systems being forced to expand and stabilize at the same time, labor turning into training data at the level of behavior itself, and state power recalibrating around capability the instant it proves consequential enough. Every transformation has a breaking point. Load can collapse a system that was never designed to bear it... or teach it where reinforcement must begin.
AI Releases & Advancements
New today
- Brex: Released CrabTrap, an open-source HTTP proxy that uses LLM-as-a-judge to secure AI agent traffic in production. (Brex)
Other recent releases
- Moonshot AI: Released Kimi Vendor Verifier, a tool for checking the accuracy and consistency of inference providers serving Kimi models. (Kimi Blog)
- Open WebUI: Released Open WebUI Desktop, a desktop app that bundles llama.cpp for local inference and can also connect to remote servers. (GitHub)
- RightNow AI: Released OpenFang, an open-source agent operating system for running tool code in WebAssembly with fuel metering. (GitHub)
- Siemens: Launched the Eigen Engineering Agent, a generally available AI engineering agent for PLC coding, HMI visualization, and device configuration workflows. (Siemens)
- Qwen: Released Qwen3.6 Max Preview, a new model now live in chat.qwen.ai. (Qwen)
- ggml-org / llama.cpp: Merged speculative checkpointing into llama.cpp for faster speculative decoding on prompts with high draft acceptance rates. (GitHub)
- MiniMax: Launched MaxHermes, a cloud sandbox agent now available. (MiniMax)
Sources
Artificial Intelligence & Technology's Reconstitution
- Ars Technica: Mozilla: Anthropic's Mythos Found 271 Security Vulnerabilities in Firefox 150
- Wired: Mozilla Used Anthropic's Mythos to Find and Fix 271 Bugs in Firefox
- Guardian: Anthropic Investigates Report of Rogue Access to Hack-Enabling Mythos AI
- BBC: Claude Mythos AI Can Be 'Net Positive' to UK Says Cyber Official
- Ars Technica: Meta Will Train AI Agents by Tracking Employees' Mouse, Keyboard Use
- iTnews: Meta to Start Capturing Employee Mouse Movements, Keystrokes
- Business Insider: Inside the AI Coding Startup Elon Musk Is Betting $60 Billion On
- The Next Web: OpenAI Recruits Cognizant and CGI to Take Codex Into Enterprise Software Shops
Institutions & Power Realignment
- Gizmodo: Trump Is Warming Up to Anthropic Again
- Business Insider: Sam Altman Opens Up About the Molotov Cocktail Attack on His Home
- Business Insider: Sam Altman Compares Anthropic's Mythos to Dropping a Bomb While Selling a Bomb Shelter
- Billboard: Anthropic Argues for Fair Use in UMG's AI Lawsuit
- Guardian: AI Hallucinations Found in High-Profile Wall Street Law Firm Filing
- Nature: AI Doom Warnings Are Getting Louder. Are They Realistic?
- Guardian: UK Could Face 'Hacktivist Attacks at Scale'
Scientific & Medical Acceleration
- Nature: Triple-Decker Solar Cells Reach Efficiency Milestone
- Nature: Personalized CRISPR Therapies Could Soon Reach Thousands
- ScienceDaily: Two Common Drugs May Reverse Fatty Liver Disease
- Nature: US Speeds Research Into Mind-Altering Drugs Including Ibogaine
Economics & Labor Transformation
Infrastructure & Engineering Transitions
- Canary Media: US Judge Halts Trump Admin's Blockade on New Wind and Solar Projects
- Utility Dive: Sudden Data Center Load Losses Prompt NERC Alert
- Canary Media: The World Is Embracing Offshore Wind - Even as the US Retreats
- Canary Media: A New Thermal Battery Could Help This Minnesota Campus Electrify Heat
- Utility Dive: Virginia Public Power Providers Embrace Distribution-Connected Batteries
- Utility Dive: Kentucky Utilities Eye 266-MW Pumped Storage Project
- Canary Media: Why Smartphone Cameras Could Unlock Cheaper, Faster Rooftop Solar
- Canary Media: Fervo Energy Unveils New Power Plant Details in IPO Filing
- Utility Dive: Rivian, Redwood Materials Announce Energy Storage Partnership
The Century Report tracks structural shifts during the transition between eras. It is produced daily as a perceptual alignment tool - not prediction, not persuasion, just pattern recognition for people paying attention.