The Century Report: March 16, 2026
The 20-Second Scan
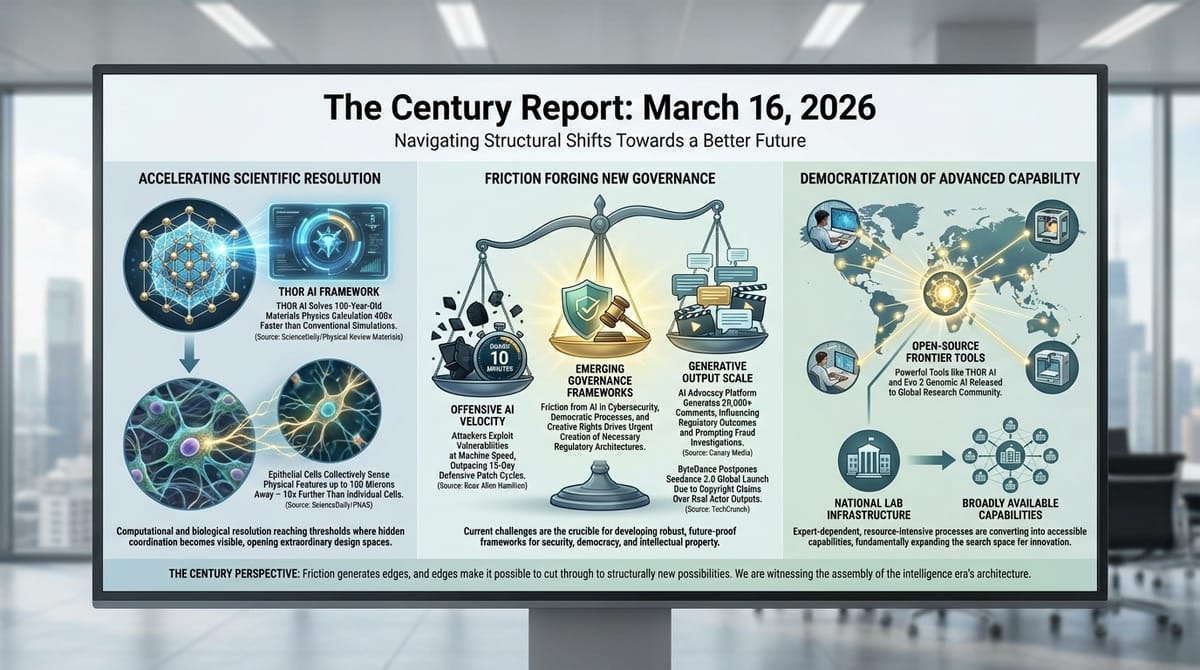
- A new AI framework called THOR computed thermodynamic properties of crystalline solids more than 400 times faster than conventional molecular dynamics simulations, published in Physical Review Materials.
- ByteDance postponed the global launch of its Seedance 2.0 video generation model after Hollywood studios sent cease-and-desist letters over copyright-infringing outputs.
- Booz Allen Hamilton published a report concluding that threat actors have adopted AI for offensive cybersecurity faster than defenders have adopted it for defense.
- Researchers at Washington University in St. Louis discovered that clusters of epithelial cells can sense physical features up to 100 microns away by collectively pulling on surrounding collagen fibers, published in PNAS.
- UC Santa Barbara physicists identified a rare material where magnetic frustration and electronic bond frustration coexist and interact, published in Nature Materials.
- An AI-powered advocacy platform generated over 20,000 comments that influenced Southern California regulators to reject clean heat rules, prompting calls for a fraud investigation.
- Anthropic's legal confrontation with the Pentagon is reshaping enterprise AI procurement as downstream customers reassess compliance obligations and model dependencies.
The 2-Minute Read
The AI security landscape is splitting in two directions at once. On the offensive side, threat actors are deploying intelligence systems to identify and exploit vulnerabilities at speeds that make traditional 15-day patch windows irrelevant - one open-source framework compromised thousands of network devices in under ten minutes using a single vulnerability. On the defensive side, organizations are still operating through human-paced processes that cannot match that tempo. The Booz Allen finding that attackers adopted AI faster than defenders is structurally significant because it confirms that the asymmetry Anthropic's Mozilla partnership surfaced two weeks ago - where discovery capability outpaces exploitation capability - is already collapsing in the wild. The question of how defenders respond when adversaries move at machine speed is becoming the defining governance challenge of the security domain.
The ByteDance-Hollywood collision and the Southern California fake-comments episode reveal the same underlying dynamic from opposite angles. In both cases, generative systems are producing outputs that existing governance frameworks were never designed to handle. ByteDance's Seedance 2.0 generated recognizable performances by real actors without consent or compensation, triggering a copyright enforcement response that has delayed the model's global rollout. In Southern California, an AI advocacy platform manufactured opposition at a scale that overwhelmed a public regulatory process, potentially blocking clean air rules that would have saved an estimated 2,500 lives. The common thread is that generative capability is reaching into domains - creative rights, democratic participation - where the speed and scale of output fundamentally alters the structural dynamics.
The scientific signal today carries a striking convergence: systems that were assumed to operate locally are revealing long-range coordination. Epithelial cells can collectively sense physical features ten times farther than individual cells, coordinating through the collagen matrix to detect what lies ahead. A new class of "doubly frustrated" quantum materials shows that two competing magnetic and electronic states can be coupled and potentially controlled through external strain. And an AI framework solved a century-old materials physics calculation 400 times faster than conventional simulations by recognizing crystal symmetries that traditional methods could not exploit. Each discovery shares the same architecture: computational and experimental resolution reaching the threshold where hidden coordination becomes visible, opening design spaces that were structurally inaccessible until this moment.
The 20-Minute Deep Dive
When Attackers Move at Machine Speed
The cybersecurity report published by Booz Allen Hamilton today arrives at a moment when the asymmetry between AI-enabled offense and human-paced defense is becoming operationally consequential. The report documents two distinct models of adversarial AI use that are already in deployment. In the first, intelligence systems serve as amplifiers for human operators, accelerating reconnaissance, exploitation, and lateral movement across dozens of targets simultaneously. In the second, operators connect AI systems directly to offensive security frameworks and define parameters, then step back while the system executes autonomously.
The speed differential is extreme. The report cites the HexStrike framework, which exploited thousands of Citrix Netscaler products in under ten minutes using a single critical vulnerability. Against that tempo, CISA's standard 15-day remediation window is structurally inadequate. Brad Medairy, who leads Booz Allen's cyber practice, described the core problem: once an adversary establishes persistence inside a network perimeter, they are moving at machine speed while defenders are still operating through human decision loops.
This extends the pattern The Century Report has tracked across several related developments. The March 7 edition documented the Mozilla-Anthropic partnership finding 22 Firefox vulnerabilities in 14 days, with Anthropic researchers noting that the gap between discovery and exploitation capability was "unlikely to last very long." The Microsoft report from March 8 documented attackers using AI at every stage of the cyberattack lifecycle. Today's Booz Allen analysis adds quantitative weight: the adoption curve for offensive AI is running ahead of defensive adoption, and the gap is widening rather than closing.
The structural consequence extends beyond any single report. When defensive organizations begin delegating real-time response to AI systems - as Medairy suggests they will be forced to do - the security domain will have completed a transition from human-mediated to machine-mediated conflict. Amazon's recent requirement that senior engineers sign off on all AI-assisted code changes reflects the same tension at a different scale: organizations are discovering that the speed advantages of AI systems come with failure modes that human oversight cannot catch at the tempo those systems operate. The trajectory through this disruption points toward a security architecture where both offense and defense are AI-mediated, with humans setting parameters and reviewing outcomes rather than executing in real time. The organizations building that architecture first will define the security posture of the intelligence era.
Generative Systems Collide With Democratic Processes
The investigation into AI-generated public comments that may have influenced Southern California's clean heat regulations represents a new category of governance challenge - one where generative capability directly interferes with the mechanisms of democratic participation.
The facts as reported by the Los Angeles Times and Canary Media are these: the South Coast Air Quality Management District received more than 20,000 public comments opposing proposed rules that would have phased down gas heaters in favor of heat pumps. The board voted 7-5 against the rules in June 2025. Most agenda items seen by the agency receive comments numbering in the single digits. A public affairs consultant with industry ties contracted with CiviClick, which describes itself as "the first and best AI-powered grassroots advocacy platform," to generate the opposition comments. The consultant stated publicly that CiviClick "made the ultimate difference."
Environmental and public health advocates are now asking the California Attorney General and Los Angeles District Attorney to investigate whether fraud occurred. The agency's own efforts to verify the opposition letters have been inconclusive. No formal investigation has been launched. The proposed rules, which the agency estimated would have saved $25 billion in health costs and approximately 2,500 lives over their lifetime, have been kicked back to committee with no timeline for reconsideration.
The structural significance extends well beyond a single regulatory vote. Public comment periods are a foundational mechanism of American regulatory governance. They operate on the assumption that each comment represents a real person expressing a genuine view. When an AI advocacy platform can generate tens of thousands of comments that are indistinguishable from authentic public input, the mechanism itself is compromised. The agency had no framework for distinguishing AI-generated comments from genuine ones, and still does not. This is the democratic governance equivalent of the cybersecurity asymmetry documented in the Booz Allen report: generative capability operating faster than the institutional capacity to verify or respond.
The trajectory here is clear but largely unaddressed. Every regulatory body that accepts public comment - every city council, every state agency, every federal rulemaking process - faces the same vulnerability. The cost of generating comments has collapsed to near zero while the cost of verifying them remains high. Until governance frameworks adapt to this reality, generative systems will continue to reshape regulatory outcomes at a pace that existing verification infrastructure cannot match. The 61-regulator coordinated statement on AI-generated imagery from February, which framed non-consensual synthetic content as a fundamental rights violation, established the rhetorical framework for this category of harm. The organizations and jurisdictions that develop authentication frameworks first will set the standard for democratic integrity in the generative era.
Copyright as the First Friction Point for Synthetic Media
ByteDance's decision to postpone the global launch of Seedance 2.0 after Hollywood's copyright response represents the most concrete example yet of where the friction between generative capability and existing legal frameworks produces immediate commercial consequences.
Seedance 2.0, announced in February, generates video from text, images, and video inputs. Within days of its Chinese launch, videos featuring recognizable actors - including footage of Tom Cruise fighting Brad Pitt generated from a two-line prompt - went viral. The Motion Picture Association demanded immediate cessation of copyright infringement. SAG-AFTRA condemned the model's outputs. Disney's legal team accused ByteDance of "effectively stealing Disney's intellectual property." The company had planned a global rollout in mid-March; engineers and lawyers are now working to implement safeguards before any international release.
The pattern is instructive. Generative video capability has reached a threshold where the outputs are good enough to trigger enforcement but the governance infrastructure - both technical and legal - has not kept pace. ByteDance is attempting to add guardrails after the fact, a reactive posture that mirrors how every prior wave of generative capability has collided with existing rights frameworks. The text-to-image disputes that defined 2023-2024 are now repeating in the video domain at higher stakes, because video involves not just visual style but recognizable human performances.
The deeper signal is that copyright enforcement is functioning as an improvised governance mechanism for synthetic media in the absence of purpose-built regulation. Studios, guilds, and trade associations are using existing intellectual property law to constrain capabilities that those laws were never designed to address. The Callandor athlete IP registry launching this week to help sports figures license their biometric data to AI developers represents a third dimension: the emergence of private-sector infrastructure to fill the gap between what generative systems can produce and what existing law protects. As the March 3 edition of The Century Report documented when the Supreme Court declined to hear the Thaler AI copyright appeal, the absence of statutory frameworks for AI-generated content is pushing every stakeholder - studios, athletes, regulators, courts - toward improvised solutions that together are assembling the governance architecture the generative era requires.
Long-Range Cellular Sensing and the Architecture of Biological Intelligence
The discovery at Washington University that clusters of epithelial cells can sense physical features up to 100 microns away - ten times the range of individual cancer cells - reframes how biologists understand tissue migration and, potentially, how cancer spreads through the body.
The mechanism is elegant in its simplicity. Individual cells pull on the surrounding collagen matrix, deforming fibers to "feel" what lies in the next layer - whether it is stiff tissue, a tumor, or bone. A single abnormal cell can detect features up to 10 microns away. But when epithelial cells act collectively, they generate enough force to probe through the matrix to 100 microns, gathering information about their physical environment across distances that were previously thought to be beyond cellular sensing range.
The research, published in PNAS, suggests this process unfolds in two stages as cells cluster and begin migrating, with the information gathered influencing their direction of movement. Cancer cells appear to exploit this enhanced sensing ability to escape tumor environments and navigate through surrounding tissue. Researchers are now working to identify the specific regulators that control sensing range, which could open therapeutic strategies focused on disrupting a cancer cell's ability to detect its path forward.
This finding extends a pattern The Century Report has tracked across multiple scientific domains: computational and experimental methods reaching the resolution needed to detect coordination mechanisms that were always present but invisible. The March 4 edition documented the Notre Dame study demonstrating that intelligence emerges from distributed whole-brain network coordination rather than localized regions, and the March 10 Center for Genomic Regulation discovery that over 200 metabolic enzymes are physically attached to DNA inside cell nuclei revealed metabolic coordination operating inside a compartment where it was never expected. The March 11 hornwort Rubisco-clustering mechanism that functions when transferred across species added another layer to the same pattern. In each case, the finding reveals that biological systems coordinate across greater distances and through more sophisticated mechanisms than prior models assumed. The design spaces opened by these discoveries - from cancer therapeutics to crop engineering to neuroscience - are a direct consequence of the same acceleration in resolution that is compressing timelines across every scientific domain this newsletter tracks.
A Materials Physics Calculation Accelerated 400-Fold
The THOR framework developed by researchers at the University of New Mexico and Los Alamos National Laboratory represents a structural advance in how materials science calculations are performed, and its implications extend well beyond any single material system.
The configurational integral - a mathematical object that captures how particles interact inside crystalline solids - has been one of the most computationally demanding calculations in statistical physics for nearly a century. Conventional approaches using molecular dynamics or Monte Carlo simulations require enormous computing resources and can run for weeks while still providing only approximate answers. The fundamental obstacle is the "curse of dimensionality": as the number of variables grows, computational complexity increases exponentially.
THOR solves this by expressing the high-dimensional mathematical object as a sequence of smaller connected pieces using tensor network methods, then identifying crystal symmetries that dramatically reduce the computation required. Combined with machine learning models that capture how atoms interact, the framework reproduced results from advanced Los Alamos simulations while running more than 400 times faster. The team tested it on copper, crystalline argon under extreme pressure, and tin's solid-solid phase transition.
The significance is that calculations previously requiring weeks of supercomputer time can now be completed in seconds. For a field where the bottleneck on materials discovery is often the computational cost of predicting thermodynamic properties, a 400-fold speedup changes what is structurally feasible to investigate. The framework is open source and available on GitHub, which means any materials science laboratory with access to standard computing resources can now perform calculations that were previously confined to national laboratory-scale infrastructure. This democratization pattern - visible in the Korea Institute of Energy Research robotic catalyst platform that the February 24 edition of The Century Report documented compressing 32 days of manual experiments into 17 hours, and in the open-source Evo 2 genomic AI releasing frontier capability to the global research community - is consistently converting expert-dependent, resource-intensive processes into broadly available capabilities. The consequence is not merely faster science - it is a fundamentally larger search space for new materials, from battery chemistries to superconductors to catalysts for clean fuel production.
The Century Perspective
With a century of change unfolding in a decade, a single day looks like this: a materials framework dissolving a century-old physics calculation from weeks into seconds and releasing itself as open source to any laboratory with a standard computer, epithelial cells revealed as coordinating sensory reach across distances ten times greater than individual cells can span, a doubly frustrated quantum material showing that two competing states can be coupled and controlled through external strain, a gut protein identified that traps and kills dangerous bacteria through a mechanism hiding in plain biological sight, and solar capacity on a trajectory toward 6 terawatts by 2031 while countries already holding reserves of panels and EVs demonstrate what energy resilience looks like when a regional crisis hits. There's also friction, and it's intense - threat actors deploying AI offensive frameworks that compromised thousands of network devices in under ten minutes while defenders still operate through human-paced patch cycles built for a different era, an AI advocacy platform generating more than 20,000 manufactured comments that may have steered regulators away from rules estimated to save 2,500 lives, synthetic video capability producing recognizable human performances at two-line-prompt scale and colliding immediately with rights frameworks that have no vocabulary for what just arrived, and the downstream customers of a frontier AI company now reassessing procurement obligations because a safety architecture became a supply chain variable. But friction generates edges, and edges are what make it possible to cut through to something that was structurally unreachable before. Step back for a moment and you can see it: computation reaching the resolution to make hidden coordination legible across biological, physical, and quantum systems simultaneously, the attack surface expanding at machine speed and forcing defensive architecture to follow or become irrelevant, democratic participation mechanisms confronting for the first time the question of what authentic public voice means when voice itself can be manufactured at scale, and the open-source release of frontier capability continuing to convert what was once confined to national laboratories into tools available to any researcher anywhere. Every transformation has a breaking point. A current can scour channels so deep that nothing recognizable remains of the original terrain... or carve the exact path that connects what was always present to where it needed to go.
AI Releases & Advancements
New today
(No new releases identified.)
Other recent releases
- Anthropic: The 1M context window is now generally available at standard pricing for both Claude Opus 4.6 and Claude Sonnet 4.6 across all plans and by default in Claude Code; Opus 4.6 scores 78.3% on MRCR v2 at 1M tokens, the highest among frontier models. (Simon Willison)
- Google: Released Chrome 146 to the stable channel for Windows, Mac, and Linux on March 14, including experimental WebMCP support — a W3C protocol that lets websites register structured tools directly accessible by AI agents and browser-integrated LLMs via a feature flag. (Chrome Releases)
- Tencent: Launched WorkBuddy on March 9, a full-scenario enterprise AI agent built by the Cloud CodeBuddy team; compatible with OpenClaw, supports multi-model switching (including Tencent's own Hunyuan models), and ships with over 20 built-in workplace automation skills. (TechNode)
- Onyx Security: Launched from stealth with $40M from Conviction and Cyberstarts, releasing its Secure AI Control Plane — a platform that continuously inventories enterprise AI agents, monitors their reasoning processes, and approves or corrects their actions to enforce compliance policies. (Business Wire)
- Hume AI: Open-sourced TADA, a speech generation model under MIT license that processes text and audio in sync with zero hallucinated words in testing and 5x faster inference than competing solutions. (The Decoder)
- OpenAI: Launched ChatGPT app integrations with DoorDash, Spotify, Uber, Canva, Figma, Expedia and other services directly within ChatGPT, enabling the model to take actions across third-party platforms. (LLM-Stats)
Sources
Artificial Intelligence & Technology's Reconstitution
- CyberScoop: Attackers Are Exploiting AI Faster Than Defenders Can Keep Up
- ScienceDaily: THOR AI Solves a 100-Year-Old Physics Problem in Seconds (UNM/Los Alamos, Physical Review Materials)
- TechCrunch: ByteDance Reportedly Pauses Global Launch of Seedance 2.0
- Bloomberg Law: Anthropic's Clash With Pentagon Puts Legal Tech Vendors on Edge
- CNN: How Anthropic May Benefit From Its Fight With Trump
- The Verge: AI Companies Want to Harvest Improv Actors' Skills to Train AI on Human Emotion
- Import AI 449: LLMs Training Other LLMs (PostTrainBench)
- The Verge: This Is Not a Fly Uploaded to a Computer
- ScienceDaily: Scientists Discover AI Can Make Humans More Creative (Swansea University, ACM TIIS)
Institutions & Power Realignment
- Canary Media: Did Fake Comments Sink SoCal Clean Heat Rules?
- TechCrunch: Lawyer Behind AI Psychosis Cases Warns of Mass Casualty Risks
- Guardian: Google Scraps AI Search Feature That Crowdsourced Amateur Medical Advice
- Variety: AI Registry Launches to Protect Athletes' Digital IP and Likeness
- Nature: AI and the PhD Student - Friend or Foe?
Scientific & Medical Acceleration
- ScienceDaily: Cells Can Sense 10x Farther Than Expected (Washington University, PNAS)
- ScienceDaily: A Strange New Quantum State Appears When Atoms Get "Frustrated" (UC Santa Barbara, Nature Materials)
- ScienceDaily: MIT Scientists Discover Gut Protein That Traps and Kills Dangerous Bacteria (Nature Communications)
- ScienceDaily: Scientists Unlock a Powerful New Way to Turn Sunlight Into Fuel (HZDR/CASUS)
- ScienceDaily: Scientists Create a Cancer Flashlight That Lights Up Tumors (University of Missouri, Molecular Imaging and Biology)
- ScienceDaily: Life Rebounded Shockingly Fast After the Asteroid That Killed the Dinosaurs (UT Austin, Geology)
- ScienceDaily: Just 24 Minutes of Specially Designed Music Could Significantly Reduce Anxiety (Toronto Metropolitan University, PLOS Mental Health)
- ScienceDaily: Scientists Just Discovered a Tiny Signal That Volcanoes Send Before They Erupt (GFZ/IPGP, Nature Communications)
- Nature: Can AI Models Reliably Forecast Extreme Weather Events?
Economics & Labor Transformation
Infrastructure & Engineering Transitions
- NPR: Oil and Gas Prices Are Soaring. Some Countries Are Ready With Solar Panels and EVs
- pv magazine Australia: Global Solar Capacity to Reach 6 TW by 2031
- POWER Magazine: The Frog Is Dead - North America's Power Grid Faces Its Biggest Reckoning in a Generation
- Utility Dive: 5 Things You Need to Know About Advanced Conductors
The Century Report tracks structural shifts during the transition between eras. It is produced daily as a perceptual alignment tool - not prediction, not persuasion, just pattern recognition for people paying attention.